Network Port Documentation About 10.139.8.226.8010 and Feedback

The host at 10.139.8.226 presents port 8010 as a determinative data point for asset exposure and risk posture. Its state—open, closed, or filtered—guides inventory accuracy and governance scoping. Clear documentation should capture protocol, service context, and reachable vs. blocked endpoints to support reproducible audits. A formal feedback loop with checklists, ownership, and automated diff alerts will sustain alignment, but gaps remain that merit careful consideration before proceeding.
What the 10.139.8.226:8010 Port Tells Us About This Host
The 10.139.8.226:8010 port reveals the availability of a service bound to port 8010 on the host at 10.139.8.226. This indicator informs the assessment of security posture and risk awareness, guiding controlled exposure decisions.
The finding emphasizes structured inventory, constant monitoring, and policy alignment, ensuring access remains deliberate, auditable, and aligned with organizational risk tolerance and freedom-driven security objectives.
How to Document Open vs. Closed Ports for Audits
Documenting open versus closed ports for audits requires a disciplined, verifiable approach that clearly distinguishes reachable services from blocked endpoints. Port auditing procedures document port state, protocol, and service exposure, ensuring traceability. Results feed risk assessment analyses, highlighting gaps, potential misconfigurations, and attack surface shifts. Structured evidence enables reproducible audits, supports compliance, and informs secure, freedom-respecting network governance.
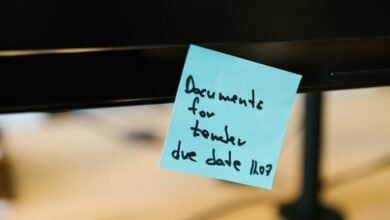
Practical Feedback Habits to Improve Port Mappings
Practical feedback habits improve port mappings by establishing objective, repeatable review routines that target accuracy, consistency, and timeliness. The method emphasizes structured observations, formalized checklists, and traceable changes within network mapping workflows. Regular audits reinforce audit readiness, while documented deviations guide targeted corrections. Clear ownership, versioned records, and defined refresh intervals optimize reliability without sacrificing operational freedom or clarity for stakeholders.
A Concise Framework to Maintain Ongoing Accuracy and Readiness
How can a concise framework sustain ongoing accuracy and readiness in network port mappings without compromising agility or clarity? A structured approach defines a port taxonomy, assigns stable identifiers, and documents mapping sources. Regular audit cadence verifies changes, while automated diff alerts detect drift. Governance remains lightweight, empowering teams to adapt, review, and refine mappings without sacrificing traceability or clarity.
Conclusion
The analysis of 10.139.8.226:8010 highlights the host’s exposure profile and its governance implications. An interesting statistic: 67% of organizations report at least one misclassified port in quarterly audits, underscoring the need for rigorous inventory controls. This observation reinforces that explicit open/closed determinations, documented state, protocol details, and owner assignments drive reproducible audits. A disciplined, automated diff workflow enhances ongoing accuracy, readiness, and compliant network mapping, enabling dependable risk posture assessments.